Business Impact and Considerations
Addressing these air-gapped infrastructure challenges was critical for this client’s operational security and mission readiness since:
- Network connectivity may expose classified systems to cyber threats and espionage risks
- Manual deployment processes can create security vulnerabilities and operational delays
- Monolithic architecture may limit rapid feature delivery and system resilience
- Inability to adopt modern DevOps practices within secure, isolated environments
- Infrastructure complexity can prevent efficient scaling and service management
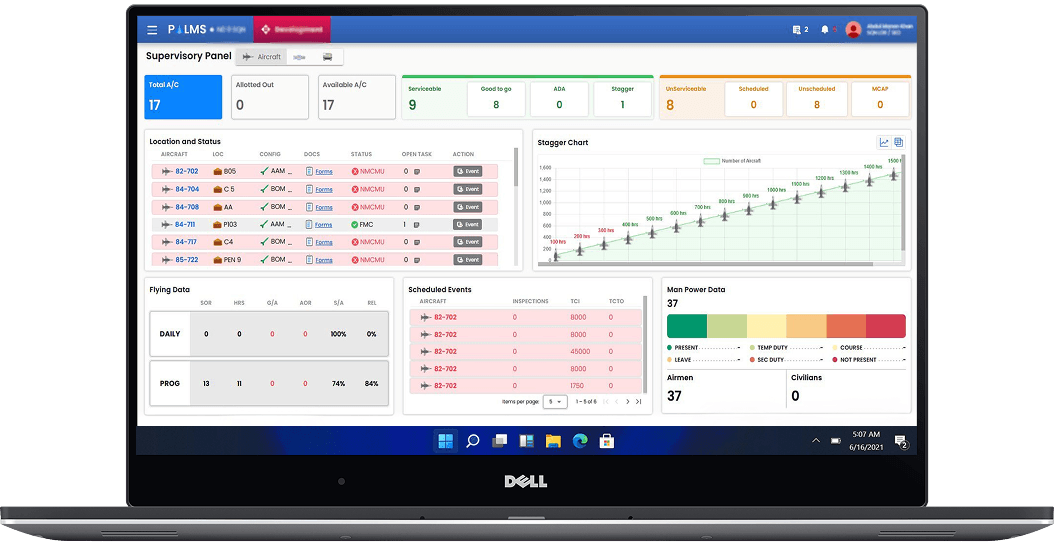
Air-Gapped Kubernetes Architecture
DPL designed and implemented a sophisticated air-gapped Kubernetes platform deployed entirely on-premises within PAF’s secure, classified data center. The solution leverages containerization, zero-trust security principles, and offline-capable DevOps automation to deliver modern cloud-native capabilities in a completely isolated environment.
1.Air-Gapped Kubernetes Cluster with Rancher
- Rancher Kubernetes Engine (RKE2) for providing air-gap-compatible Kubernetes distribution
- Multi-master high-availability cluster configuration with automated failover
- Local container registry (Harbor) for hosting all application and system images
- Kubernetes control plane secured with certificate-based authentication and RBAC
- Network policies enforcing microsegmentation between namespaces and pods
- Local Helm chart repository for application package management
2. GitLab On-Premises for Offline CI/CD
- GitLab Enterprise Edition deployed on-premises with all CI/CD capabilities
- GitLab Runners configured for Kubernetes executor enabling containerized builds
- Integrated container registry for storing build artifacts and Docker images
- Automated pipeline stages: build, test, security scan, deploy to Kubernetes
- Environment-based deployment workflows (dev, staging, production)
- Pipeline caching and artifact storage for faster build times
- GitLab Pages for internal documentation and API references
3. Zero-Trust Security Architecture
- Istio service mesh to provide mutual TLS (mTLS) for all service-to-service communication
- Certificate-based authentication using internal Certificate Authority (Vault PKI)
- Network-level isolation with VLANs, firewalls, and Kubernetes network policies
- Container image scanning with Trivy for vulnerability detection
- Pod Security Policies (PSP) and OPA Gatekeeper for enforcing security constraints
- Secrets management with HashiCorp Vault integrated with Kubernetes
- Falco runtime security monitoring for detecting anomalous container behavior
4. Containerized Microservices Platform
- Microservices architecture for decomposing monolithic applications into containerized services
- Service mesh (Istio) for providing traffic management, load balancing, and circuit breaking
- Kubernetes Ingress controllers for external traffic routing and SSL termination
- Horizontal Pod Autoscaler (HPA) for automatically scaling based on CPU and memory metrics
- StatefulSets for databases and persistent workloads with stable network identities
- ConfigMaps and Secrets for environment-specific configuration management
5. Offline Observability Stack
- Prometheus for metrics collection and alerting from Kubernetes and applications
- Grafana dashboards to provide real-time visibility into cluster and application health
- EFK Stack (Elasticsearch, Fluentd, Kibana) for centralized log aggregation
- Jaeger distributed to trace tracking requests across microservices
- Kube-state-metrics and node-exporter to expose Kubernetes cluster metrics
- AlertManager routing critical alerts to operations teams via internal channels
6. Air-Gap Package Management and Updates
- Local YUM/APT mirror repositories for OS packages and security updates
- Harbor container registry with replication policies for multi-cluster sync
- ChartMuseum for hosting Helm charts for application deployments
- Nexus Repository Manager for Maven, NPM, and PyPI artifacts
- Air-gap bundle management for Kubernetes version upgrades
- Automated vulnerability scanning of all packages before deployment